Detect payment card testing as it happens.
Alert your team in seconds.
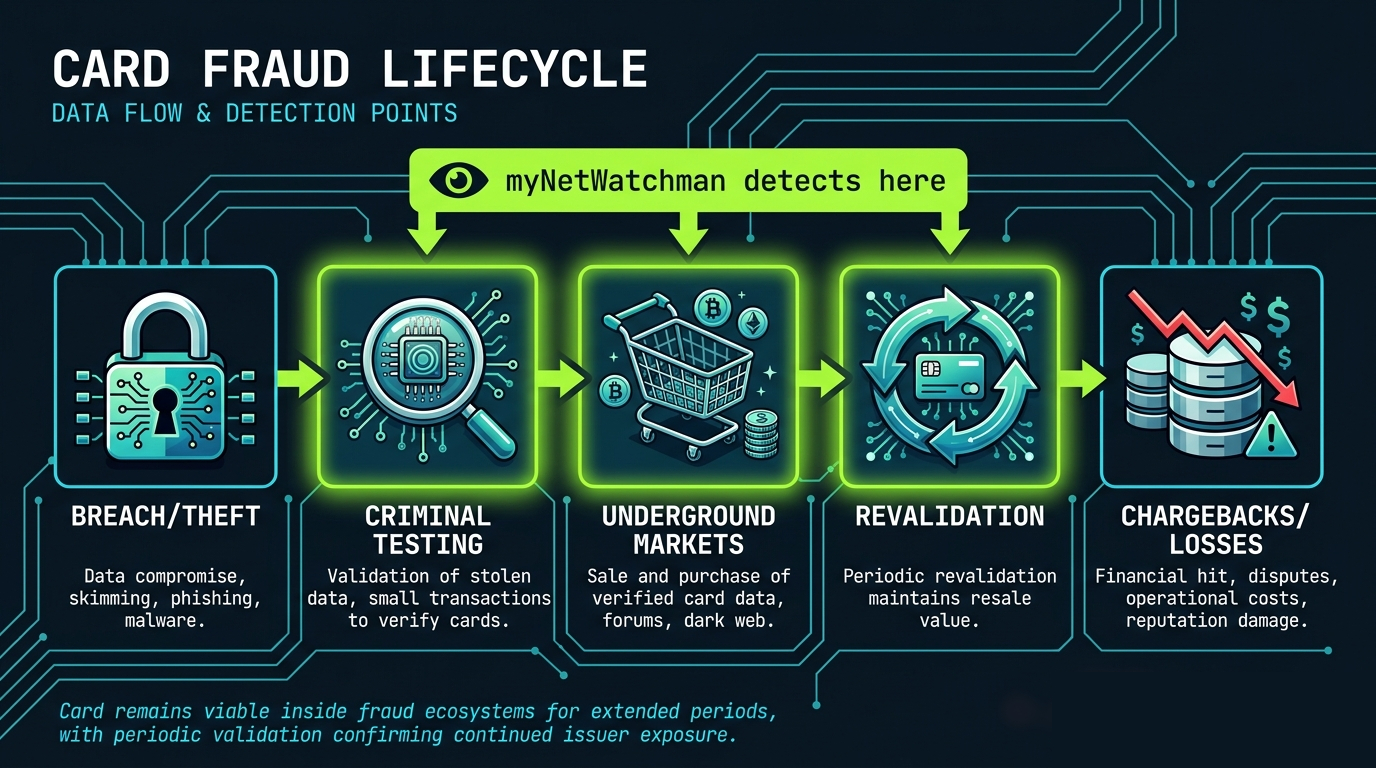
myNetWatchman BIN Monitoring detects compromised cards during the testing phase — with a 25-day average lead time over underground markets. You intervene before monetization. Losses never happen.

We see payment card testing at the earliest point in the fraud lifecycle.
The testing phase is the optimal intervention window — fraudster intent is confirmed, losses haven't occurred, and issuer action can still change the outcome.
"Detection at the testing stage is early enough to prevent monetization, yet late enough to avoid the noise and false positives associated with static exposure data."
— Economics of Card Testing, myNetWatchman, January 2026
Seconds-Level Detection
Detection occurs during the testing stage, often seconds after the first probing attempt, derived from fraudster-infiltrated infrastructure.
Cross-Merchant Visibility
Monitors testing across merchants that never send issuer authorizations — providing visibility into activity that would otherwise remain completely unseen.
All Card Types Covered
Coverage across consumer, premium, private-label, commercial, gift, and debit cards. Debit and gift cards show the highest testing volumes — both fully monitored.
BIN-Level Intelligence
Identify entire BIN clusters under attack, not just individual cards. Enables portfolio-level risk management and targeted mitigation.
Near-Zero False Positives
Alerts tied to confirmed criminal intent — avoid disrupting legitimate cardholders while stopping fraud with precision.
API or Webhook Delivery
Data delivered via API or webhook. Integration typically completed in days alongside your existing fraud infrastructure.
Where myNetWatchman intervenes.
Most fraud tools operate at the end of the lifecycle. We operate at the beginning — at the testing stage, before losses occur.
Real-world performance data.
Whatever they call it, we monitor it.
Payment card fraud goes by many names in criminal networks. Our intelligence covers all of them.
How many cards in your portfolio are being tested right now?
Find out with a free Proof of Concept against your own BINs — no commitment required.
